Top suggestions for mr |
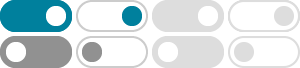
- Image size
- Color
- Type
- Layout
- People
- Date
- License
- Clear filters
- SafeSearch:
- Moderate
- Code Secure
- Secure Data
- Writing
SecureCode - What Is
Secure Code - SecureCode
Warrior - Mr Data
- Secure Data
Access - How to
Secure Data Network - Secure Code
Review - Develop
SecureCode - How to
Secure My Data - Secure Code
Library - To Secure
Important Data - Secure Package with Code
On End - Why to
Secure the Data - SecureCode
Wrrior - SecureCode
Web Page - Seure
Data - SecureCode
Practices - Writing SecureCode
Howard LeBlanc - SecureCode
Protocol - SecureCode
Warrior Icon - SecureCode
Warrior Logo - Ai Data
Security - Windows Writing SecureCode
Book - Vulnerable Code
and Secure Code - Secure Code
Warrior PNG - F-
Secure Code - SecureCode
Reviewer - Data
Privacy and Security - People Made of Code
in Cyberspace - Securing
Data - How to Secure Data
Rack Plugs - Security Codes
List - Writing SecureCode
2nd Edition PDF - Secure Code
Review Step by Step - Step to Implementing
Secure into Code - Little
Mr Data - Secure Data
Base - Secure
Coding - Cloud Data
Encryption - Secure Code
Review Process - What Is
Secure Health Code - How to Secure
More Resources - Mr Data
Password - Develop SecureCode
Avatar - Secure Code
Review Illustration - Secure
Company Data - SecureCode Warrior
Pull Request - SecureCode
Report
Some results have been hidden because they may be inaccessible to you.Show inaccessible results

 Feedback
Feedback